Automating infrastructure identity with Okta advanced server access
Introduction
Present days developing businesses revolve around the point; it is like where to stand and service. Every organization wants to be a technical organization, but the realities of the market change continuously. This unexpected change requires organizations to maintain a high speed, even users also expecting the latest ways of goods purchasing and services. And partners are searching for the latest ways to work closely without any requirement of around the world problems, with that we can change the course of working overnight. It helps to develop the speed, which attracts large organizations also. Okta training is the best way to gain complete knowledge of automation infrastructure identity with Okta advanced server access; we offer Okta training online to help those who require gaining experience.
What is Okta
It is the best foundation for a secured connection between the technologies and people; It is a famous independent supplier of enterprise identity. The identity cloud of Okta makes sure that the companies are managing their enterprise securely and their customer experience transformation. It offers almost 5.500 integrations for infrastructure suppliers and applications; it makes its customers adopt their required technologies to complete their tasks safely. Nearly 5,600 companies like getting blue, Nordstrom, Hitachi, century fox, and many put their trust in Okta to connect with their technologies and people.
Automation infrastructure identity with okta advanced server access
Companies need to face various challenges in this fastly evolving market. To break these challenges, organizations are using multiple strategic IT and intuitive security. They provide their users, employees, and partners with the ability required for their present business situations; cloud migration is accelerated as organizations search for low cost and flexibility cloud-based compute running, networking, and storage services. To improve the latest delivery services with fast scaling to meet the customer’s expectations, the software suppliers are moving to the infrastructure offered by the service providers like Amazon web services, Microsoft Azure, and the platform of google cloud.
Common barriers are shared among these strategic initiatives to implement the security speedily while the velocity of the organization is increasing. Security officers’ main task is to make their organization run at high speed without any security risk development. More than 92 per cent of IT experts described a gap between their cloud usage level and their capability of organization delivery. As the utilization of cloud developed, the cloud-based services also increased and also improved the pressure on present days CSO.
Okta advanced server access: solving a common problem with an elegant solution
It offers the cloud security complexity with urgency for speed scaling; there is no higher requirement to manage and change the organizations access. But it may lead to our operations slowdown instead of increasing its speed, and it helps to meet the needs of security. Organizations require single authentication access, which assures that the proper person can access the appropriate resources at the exact time. The aim least privilege access is the base layer in creating the model of zero-trust security. Okta explores its industry-leading identity and platform management to add the administration and server access through any hybrid infrastructure.
Okta identity leveraging helps design a single and unified IAM, which brings organizations’ servers and applications into a single roof. It is known for scalability, and it leverages automation for time streamline and manual consumption of tasks like admin users of on-boarding and off-boarding. To free up IT’s resources to install the latest services required for their employees, partners, and users. Okta ASA provides massive organizations security, it includes speed and user friendly, and they are required for access management with a high level of protection. The ASA of Okta helps to simplify the necessary developments of cold complex compliance’s like SaaS. Okta ASA also offers the internal processes to manage and track the credentials and account of user accounts of the system admin.
Enabling zero trusts server access and authentication
The keys and passwords of static are considered the weakest links in the security chain access, Okta removes these old systems, which are key-based with one-time ephemeral access. And it directly interacts with the least privileged access user profile in the database of central data identity.
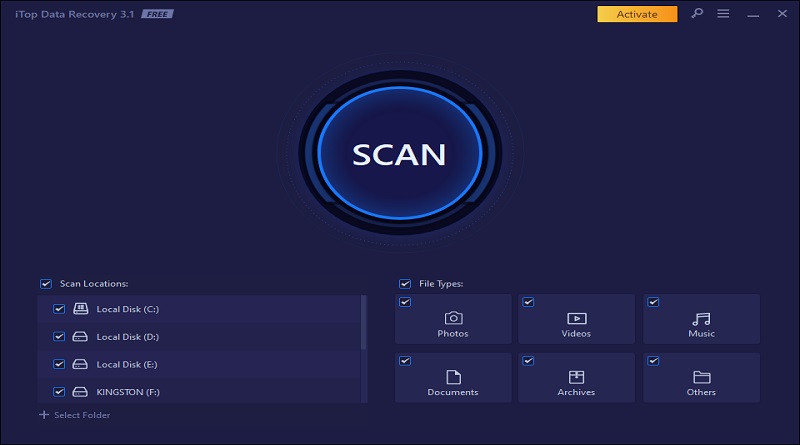
Secure login process of Okta ASA
- Using the client’s application, users can log in directly to the server from its local tools of RDP and SSH.
- The Okta authenticated users and devices, and the request is authorized against the access control, which is role-based.
- The application of a built-in client or scope for the temporary client certificate is strictly for individuals’ request.
- This certificate is used for the clients to secure SSH initiation, and the session is built with the target link.
- The sign-in event is gathered through the agent of the server and delivered for the audio log and the SEM server of 3rd party.
Instead of using the keys, the main variation between the solution and Okta ASA is based on the roles, identity, and privileged access on the server. This is used for designing the single point of control to servers; it also removes the breakage risks, which are based on the lost keys, shared accounts, and the consequences of credential sprawl.
Okta ASA addresses today’s challenges with today’s technology.
It creates advanced server access to reach the needs of business in the present days. The alternative for this integrated adoption cant reaches the speed and the requirements of the business world. Its infrastructure environment is dynamic, which helps resources spinning down and up randomly. To secure the administrative accounts, control, and credentials are not possible without creating core identity links. The PAMY vendors of the access management identify them with particular credentials, but it lacks the main control pane. This control panel is where the permission and accesses are the tasks of customer roles; it is a manual process without the perfect link for identity and server admin of on boarding and off boarding.
It permits the malefactors to enter by keeping the doors open. The process of on boarding and off boarding is automated for users. The critical tasks are simplified, and deletes the opportunities for human errors.
Conclusion
Most organizations are migrating by learning that the cloud is a complex process; every cloud vendor uses its self-authentication system. Its usage provides the IT group and the other group of credentials to control, and the vendor risk is increased. Okta ASA relieves the organization from shifting it from one cloud vendor to another without any system authentication changes. This process provides IT and the other managed credentials, but the vendor’s risk is increased. For successful functioning of the boxing with the amazon web services, the google cloud platform, Microsoft Azure, etc., its integration permits the security teams to design the authentication under a single roof.