Understanding Insider Attacks And How To Keep It From Happening
Threats to your company’s IT infrastructure can come from anywhere; from internal members to external sources, there are many possibilities.
While most organisations have measures like robust cyber security, restricted access and data security plans in place alongside other IT Support Solutions, insider attacks cannot be underestimated.
What Are Insider Attacks?
An insider attack is when someone who has internal access to your company’s data and servers uses their credentials to misuse information and hurt your organisation.
From disgruntled employees and ex-members to business partners or board members, an insider attack can come from anywhere and leave your company and its data exposed. This means that, although current employees may wrongly use their access controls to harm the company, they are not the only source that can be responsible for an insider attack.
With the rapid increase in the number of insider attacks faced by companies, keeping yourself aware can help you safeguard your organisation and keep your confidential data safe.
That said, consider working with an IT support provider in Northampton or whichever area you are based at, for better protection of your organisation.
The Different Types Of Insider Attacks
Since there are many possible sources for insider attacks, there are many ways this threat can affect or impact your organisation. Here are the main types of insider attacks you need to watchout for –
1.Turncloaks
A turncloak is an insider of your company who is maliciously stealing data. In most cases, it’s an employee or partner/contractor wrongly using your information.
This means that they are abusing their credentials and accessing your information for their personal use. Since they already have an idea about the way your systems work and the organisation of your data, they have an advantage over other attackers due to this familiarity.
2.Pawns
nlike a turncloak, a pawn is an insider who unknowingly exposes the company’s system and data to a threat.From leaving a device like a company laptop to falling victim to a scam, innocent employees may get caught in the crossfire and unknowingly leak access controls and other information. This results in losses for the company as the threat leverages the situation accordingly.
3.Mole
A mole or impostor is an outsider who somehow gains access to the company’s systems and uses it for personal gain. Usually, moles pose as a member of the organisation in order to get their hands on the data and networks.
How To Protect Yourself From Insider Attacks
Protection against insider attacks requires preemptive measures, information and awareness along with robust systems in place to ensure that your company faces minimum damages.
That said, here are a few things every organisation can do to protect itself-
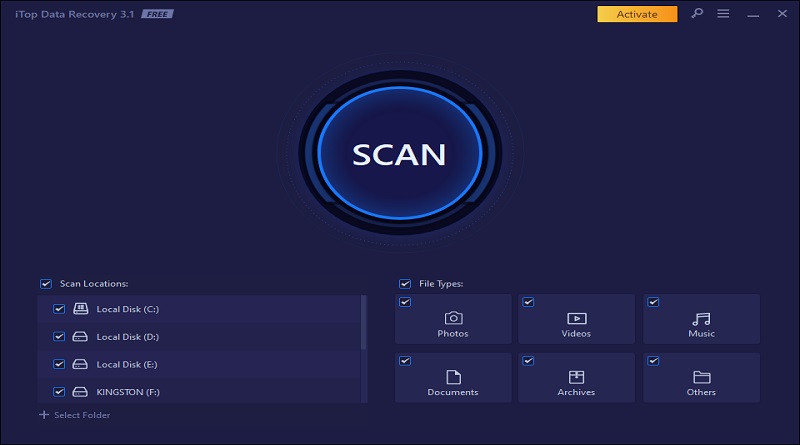
1.Adopt An Employee Monitoring Software
Implementing employee networking software is a step that you can consider for better protection and safety for your business.
With the presence of numerous online monitoring software, you could find one that better suits your security needs and implement it across the organisation. Through this, you can identify potential threats and also set rules and restrictions in place for better security.
2.Enforce Policies And Regulations
By setting clear policies and regulations in terms of data and networks, every company can enforce security measures to prevent attacks. Through this, the members of your company also get a better understanding of the way to approach the company assets to avoid susceptible methods.
Additionally, limit access to employees based on their job profiles as not everyone needs to work with all the company data.
3.Conduct Regular Training And Awareness
A major step that can prevent or help your employees stay prepared is having enough information and training to be able to identify and avoid attacks. This adds an extra layer of protection for your company, as your employees can stay aware and avoid unnecessary harm or exposure of important information.
Additionally, it also helps avoid negligence and focuses on a more careful approach with work-related operations.
To Sum Up
Not all insider attacks are on purpose, while people may harbour ill feelings and deliberately take advantage of your assets, negligence is another cause for such threats.
By staying aware and equipped with the right knowledge and implementing policies and procedures, you can ensure protection in all aspects.